CIRRUS Risk Assessment
Monitor your sensitive data to prevent breaches or compliance violations with our advanced Risk Assessment solution, including Microsoft Security Assessment.Why Risk Assessment Matters
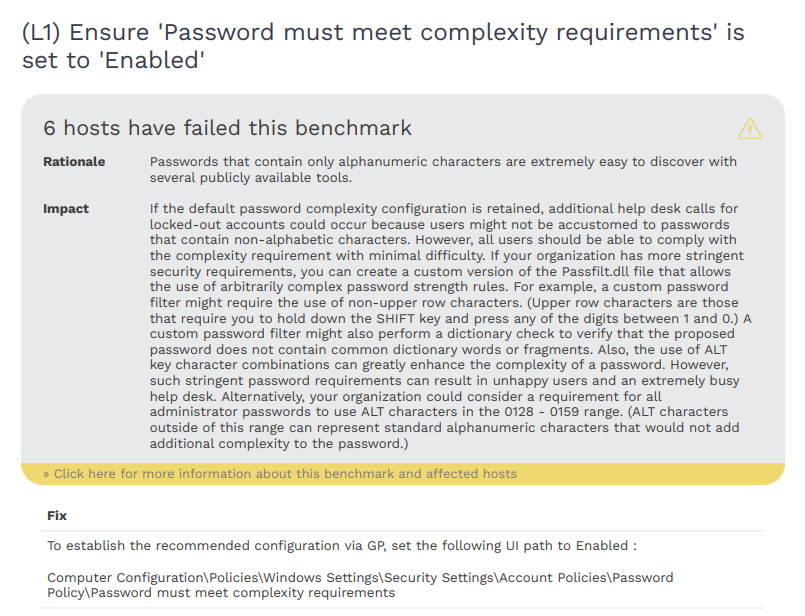
Risk assessment identifies vulnerabilities and compliance gaps, helping to safeguard sensitive data and mitigate potential threats. Below are the key benefits of conducting regular risk assessments.
Comprehensive Data Discovery
Identify sensitive data across systems with automated scans.
Real-Time Risk Identification
Detect vulnerabilities and threats as they arise.
Compliance Assurance
Stay aligned with GDPR, HIPAA, CCPA, and other regulations.
Cost and Time Efficiency
Save resources with automated processes.
Customizable Risk Scoring
Focus on the highest-impact risks with dynamic scoring.
Proactive Incident Prevention
Address risks early to prevent breaches and compliance issues.
How CIRRUS Protects You
When it Comes to Risk Assessment
Data Classification and Tagging
Sensitive data is categorized by type, location, and risk level, streamlining management and enhancing security efforts.
Risk Reporting
Detailed, customized reports are provided for both leadership and technical teams, offering clear, actionable insights.
Policy Enforcement
Data policies are implemented and maintained to ensure alignment with cybersecurity standards and compliance requirements.
Third-Party Risk Assessment
Vendors and partners are evaluated for potential security gaps, keeping the supply chain as secure as internal systems.
What Our Clients Are Saying
“The final report exceeded our expectations in terms of thoroughness and clarity. The CIRRUS platform’s ability to identify vulnerabilities and potential risks within our network was remarkable. The detailed breakdown of each identified issue and a clear assessment of its severity provided us with a comprehensive understanding of our security posture.”
Convention Center, Single Location
Director of IT, HospitalityTrending Resources
By Jason Zanetti In the world of cybersecurity, the terms “penetration testing” and “vulnerability scanning” are often used interchangeably. However, […]
By Shaun Babula As cyber threats continue to evolve, businesses in regulated industries face increasing pressure to safeguard sensitive data […]
By David Dlug After 15 years in the technology space, we’ve seen firsthand how quickly the landscape can shift, from […]
By Jason Zanetti Patch management is often viewed as a routine task, one that organizations sometimes overlook or delay in […]
By Will Colleran The shift to remote work has transformed the way organizations operate, but it has also introduced unique […]
By Shaun Babula As cyberattacks become more sophisticated and frequent, many organizations are turning to Managed Detection and Response (MDR) […]
By Stephen Stemme Penetration testing, often referred to as “pentesting,” is a cornerstone of any effective security strategy. However, to […]
By David Dlug Phishing attacks have become one of the most pervasive and dangerous threats in the cybersecurity landscape. From […]